With cyberattacks on medical devices on the rise, scholars examine regulatory challenges and solutions.
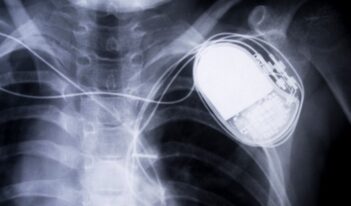
The medical device industry, which develops devices such as insulin pumps and pacemakers, experienced a digital revolution in recent years. Many medical devices now connect to the internet, phones, hospital networks, and other software, creating what has been termed the Internet of Medical Things.
With greater connectivity, however, can come greater risk.
Internet-connected medical devices are vulnerable to cyberattacks. Bad actors may be able to manipulate the devices to produce inaccurate readings or dosages, endangering patients’ health and even lives.
Indeed, roughly one in five health care organizations that suffered a cyberattack reported experiencing a subsequent increase in patient mortality rates.
Since the first known cyberattack targeting medical devices occurred in 2017, health care-focused cyberattacks have only grown more frequent. From the middle of 2020 to the end of 2021, over 80 percent of health care systems reported a cyberattack.
The U.S. Food and Drug Administration (FDA) serves as the primary regulatory body for medical device cybersecurity. FDA’s regulations require manufacturers to address cybersecurity risks, but the agency does not test devices for cyber vulnerabilities before they hit the market.
Instead, the agency regularly publishes and updates guidance documents for manufacturers and marketers. FDA first addressed the topic as early as 2005 and it continues to provide updated guidance. Earlier this year, FDA published a draft guidance document, outlining its plan to implement a zero-trust framework, which denies users access to digital services by default unless they present strong proof of identity.
In this week’s Saturday Seminar, scholars evaluate the regulatory landscape of cybersecurity for medical devices:
- FDA should establish a cost-benefit framework to evaluate the need for additional cybersecurity features in cyber-physical medical devices, according to Christopher S. Yoo and Bethany Lee in a recent University of Pennsylvania Carey Law School Institute for Law and Economics research paper. Yoo and Lee explain that cyber-physical devices defy FDA’s traditional approach to regulating safety and effectiveness. Unlike purely software or hardware devices, cyber-physical devices interact with signals from both networked devices and the physical environment. This environment is unpredictable and unbounded, with potential risks that stem from intentional, malicious actors. Yoo and Lee explore various methods of cost-benefit analyses that FDA could adopt to fill this regulatory gap, emphasizing its legal authority to consider non-therapeutic costs in assessing medical devices.
- In a chapter published in Healthcare Cybersecurity, Jennifer Archie of the law firm Latham & Watkins explores trends in the enforcement of the Health Insurance Portability and Accountability Act (HIPAA), which is the primary regulation aimed at protecting health data held by health care providers and other relevant entities. Archie argues that the Office of Civil Rights of the U.S. Department of Health and Human Services—the agency in charge of enforcing HIPAA—manages to be effective by fining companies large amounts of money. Furthermore, Archie explains that HIPAA enforcement was strengthened both by state attorneys general filing class actions and by private plaintiffs. Archie argues that it is essential that entities covered by HIPAA establish information security programs to “prevent, mitigate, and recover from breaches.”
- In an article in the Hastings Science and Technology Law Journal, Kenny E. Gutierrez, a former fellow at the Electronic Frontier Foundation, discusses the privacy and cybersecurity concerns in the mobile health application and digital wearables industry. According to Gutierrez, the sensitive medical nature of the data that such technologies analyze—such as weight, sex life, and drug use—make this practice particularly troubling. Gutierrez acknowledges that the data collection capabilities of health apps and wearables are on the forefront of precision medicine. But after surveying the United States’ sectoral privacy laws, Gutierrez argues that the industry needs a better regulatory framework as privacy and cybersecurity issues amass for users who store private medical information on these easily compromised devices.
- FDA’s current regulations have failed to protect the public from cyberattacks, argues Allee Johnson, a data privacy consultant at Ernst & Young, in an article published in the Colorado Technology Law Journal. Johnson suggests that FDA should create a safe harbor system using its current voluntary guidelines on maintaining medical devices. In this system, Johnson explains, manufacturers that comply with the guidelines would be shielded from liability. Johnson argues that this method of regulation would best balance patient interests in privacy and manufacturer interests in legal immunity for otherwise inevitable breaches.
- Cyberattacks on the health care industry are not confined to the United States, and recent legislative changes in the European Union may only make matters worse, argue Elisabetta Biasin and Erik Kamenjašević of KU Leuven University in Belgium in an article in the International Cybersecurity Law Review. Biasin and Kamenjašević note that the new laws leave certain matters—such as incident notification requirements—open to different interpretations, allowing varied and sometimes conflicting approaches across the European Union’s member states. Such fragmentation, the authors warn, could lead to uneven protection of patient data. Biasin and Kamenjašević recommend clarifying multiple phrases and terms in the laws, including “cybersecurity” itself, to create a more uniform application across the European Union.
- In a recent article in Health Policy and Technology, Nicole M. Thomasian and Eli Y. Adashi from the Warren Alpert Medical School of Brown University argue that the medical field must keep cybersecurity concerns as a high priority. Thomasian and Adashi define the major risks of cyberattacks of medical devices to include a loss of confidentiality of user information, corruption of device functionality or data, and diminished availability of the device to the user. Because FDA’s guidance does not map onto manufacturing design processes, industrial actors developed their own consensus standards, according to Thomasian and Adashi. They argue that the work of both private and public actors will be critical to improved health care cybersecurity.
The Saturday Seminar is a weekly feature that aims to put into written form the kind of content that would be conveyed in a live seminar involving regulatory experts. Each week, The Regulatory Review publishes a brief overview of a selected regulatory topic and then distills recent research and scholarly writing on that topic.